Tag: security
-
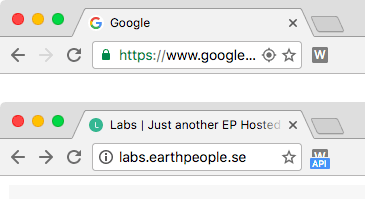
Our new tool finds “hidden” WordPress pages exposed by just released WP REST API
In December WordPress 4.7 was released. The most cool part of this release was the inclusion of the WordPress REST API. In development for quite some time it was finally included in core. The WordPress REST API is great for developers because it makes it very easy to get all pages, posts and users from…
-
Making signed requests with CodeIgniter
Recently we’ve done lots of backends for IOS apps, Flash sites, Facebook apps and such. In most cases, it’s just a matter of responding with JSON to a HTTP request, saving or fetching something from a datasource. The problem is that it’s fairly easy to sniff the request, change a few parameters and submit a…
